|
Use Case |
Integration |
ROI (Return on Investment) |
|
Deriving Item Definition from System Architecture |
The Item Definition, the starting point for every TARA, is consistently derived from the System Architecture (managed by system engineers). Benefit: The TARA is based on a current and correct representation of the system to be analyzed. Redundant data storage and resulting inconsistencies between architecture representation and TARA definition are avoided. |
Elimination of data redundancy and inconsistency, improving the quality and accuracy of the TARA, which avoids costly security design flaws later in the development cycle. |
|
Cybersecurity Requirements in Requirements Management |
Security goals and requirements identified from the TARA are directly fed into the Requirements Management System. Benefit: Cybersecurity requirements are treated equally to functional or safety requirements. A separate silo for security requirements is not created, ensuring interdisciplinary collaboration and adherence to process requirements (e.g., in the V-model). |
Reduced rework by integrating security early ("shift-left"), leading to lower development costs and ensuring product security meets market/regulatory requirements from the start. |
|
Harmonization with Safety Goals (Security Goals & Safety Goals) |
The security goals derived from the TARA are aligned and linked with the Safety Goals from functional safety management. Benefit: Consistent risk consideration in both safety and security. The integration ensures that cybersecurity measures do not unintentionally compromise the system's functional safety, and vice versa. |
Mitigating the high-cost risk of safety-security conflicts, preventing system-critical failures and the associated liability or product recall costs. |
From Silos to Synergy: The Case for Lifecycle-Integrated Cybersecurity
The traditional approach of relying on fragmented tools, manual spreadsheets, and disconnected documentation inevitably results in higher complexity, traceability gaps, and increased product risk. While many competitors attempt to address these issues through a monolithic platform approach, such strategies often reinforce silo formation by forcing cybersecurity data into a separate, proprietary environment that remains disconnected from the broader engineering context.
It needs an integrated approach that ensures that Cybersecurity is not an isolated snapshot but a living asset that safeguards the product from its initial design through to decommissioning.
To truly overcome these challenges Cybersecurity Risk Management must be seamlessly integrated into the existing ALM or PLM ecosystem, transforming Cybersecurity Risk Management from a static task into a dynamic, continuous process.
Detect, prevent and immediately react to Cybersecurity Threats.
Start adapting faster with the Cybersecurity Management Integration solution.
Cybersecurity Management Integration Use Cases
This integration begins with System Engineering, where the Item Definition for the Threat Analysis and Risk Assessment (TARA) is directly derived from the System Architecture to ensure technical consistency. It extends to Requirements Management by synchronizing Cybersecurity Goals as actionable requirements, ensuring they are tracked throughout the Development Lifecycle. Crucially, this integration bridges the gap to the Operations Phase. By linking Vulnerability Management with the design-level TARA, emerging threats in the field trigger immediate risk reassessments based on the actual system design. The following concrete use cases demonstrate real life integration scenarios.
|
Use Case |
Benefit of Best-of-Breed Integration |
ROI |
|
Risk Re-evaluation (Vulnerability Management & TARA) |
As soon as a new public vulnerability (e.g., a CVE) is detected in the Vulnerability Management System, the underlying risk in the original TARA (Threat Analysis and Risk Assessment) can be re-evaluated. Benefit: Faster reaction time and a methodologically sound, consistent risk assessment based on the design phase, without relying on manual, error-prone reviews. |
Reduced manual effort and time for risk re-evaluation faster patching/mitigation and a significant reduction in the potential cost of a security breach. |
|
Integration of Measures into Task Management |
Concrete measures and tasks derived from the TARA or other cybersecurity activities are transferred directly into the Task Management System (e.g., JIRA). Benefit: Cybersecurity activities are seamlessly integrated into the existing project planning, allowing them to be appropriately prioritized, tracked, and implemented, which avoids inefficient duplication of work and media breaks. |
Increased efficiency in project management, ensuring critical security tasks are completed on time, thereby reducing project delays and costs associated with unaddressed security risks. |
|
End-to-End Traceability (Artifact Integration) |
Relevant artifacts from the entire lifecycle – from system components to code scans – are connected to the TARA via the integration hub. Benefit: Complete, auditable traceability of all decisions and measures, which significantly simplifies compliance with standards like ISO/SAE 21434 or CRA (Cyber Resilience Act). |
Lower compliance costs, faster audit cycles, and a reduced risk of non-compliance fines or market entry delays. |
Accelerate your risk assessment process
Lightweight integration accelerates your processes
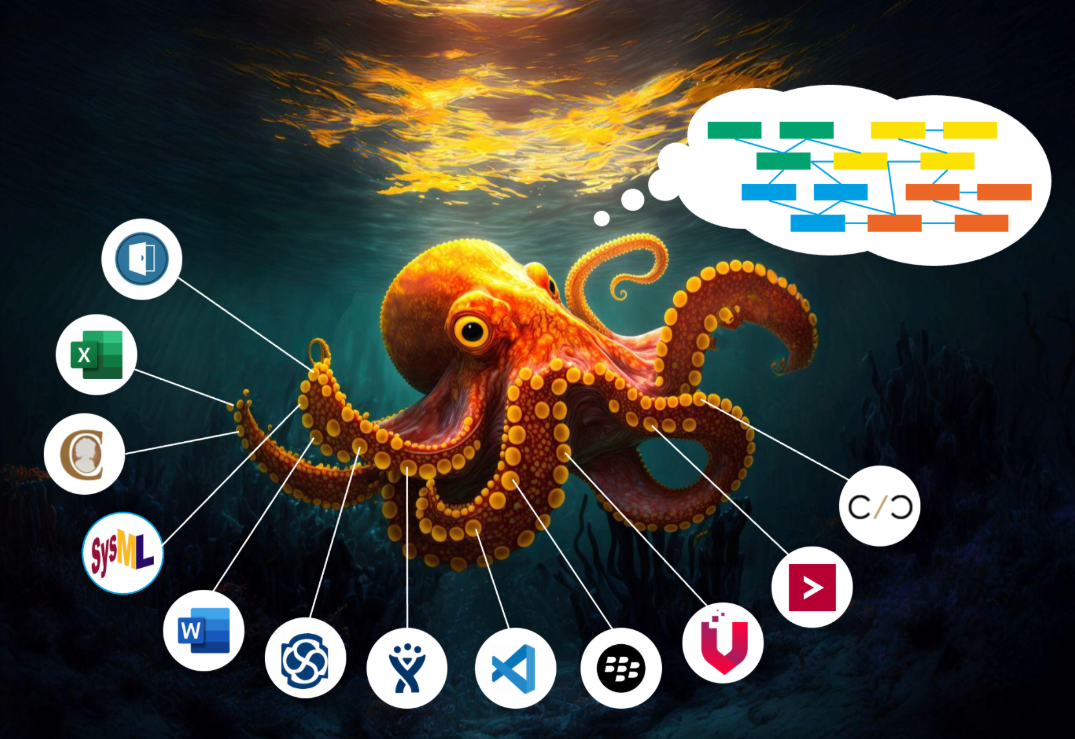
Integration allows combining the required depth (e.g., in TARA) with a critical integration into the existing tool landscape. For this solution we combine two of our powerful products itemis ANALYZE and itemis SECURE. itemis ANALYZE serves as the integration hub to implement the various Lifecycle Integrations and ensure a seamless flow of information.
Our best-of-breed cybersecurity integration solution seamlessly connects threat and risk analysis with vulnerability management. But not only: connect what you need to connect. In close collaboration with you, we develop a bespoke strategy tailored to your specific infrastructure and requirements. By detecting emerging public threats in real-time and mapping their impact on your specific products, we ensure your risk profile is always accurate and up to date - visualized on one dashboard.
Features
itemis SECURE Cybersecurity Lifecycle Integration
| Feature |
Desktop |
WebApp |
Lifecycle Integration |
|
Threat Analysis and Risk Assessment compliant to ISO/SAE 21434 |
✓ |
✓ |
✓ |
|
Interactive Attack Tree Modeling and Analysis |
✓ |
✓ |
✓ |
|
Hybrid-approach and real-time collaboration |
✓ |
✓ |
|
|
Working on multiple TARAs |
✓ |
✓ |
|
|
Collaboration and automation of processes |
✓ |
✓ |
|
|
Full V model coverage from requirements to start of production |
✓ |
||
|
integration of data and information from existing systems into knowledge graph |
✓ |
||
|
Risk-based decision-making considering multiple layers of dependencies |
✓ |
Frequently Asked Questions
It seamlessly integrates Threat Analysis and Risk Assessment (TARA) with other disciplines e.g. Vulnerability Management: by detecting emerging public threats (like CVEs) in real-time and mapping their impact on your specific products, itemis SECURE ensures your risk profile is always accurate and up-to-date, visualized on one dashboard.
Consolidating all cybersecurity activities into a proprietary platform such as a CSMS leads to the formation of a new data silo. Cybersecurity requirements become stored within the cybersecurity platform instead of the Requirements Management System, resulting in isolated, redundant and fragmented data with media breaks and inconsistencies that slow down processes.