Table of contents
Validating your data Copy link to clipboard
ANALYZE provides you different kinds of validations. They can be accessed by navigating to ANALYZE → Validation.
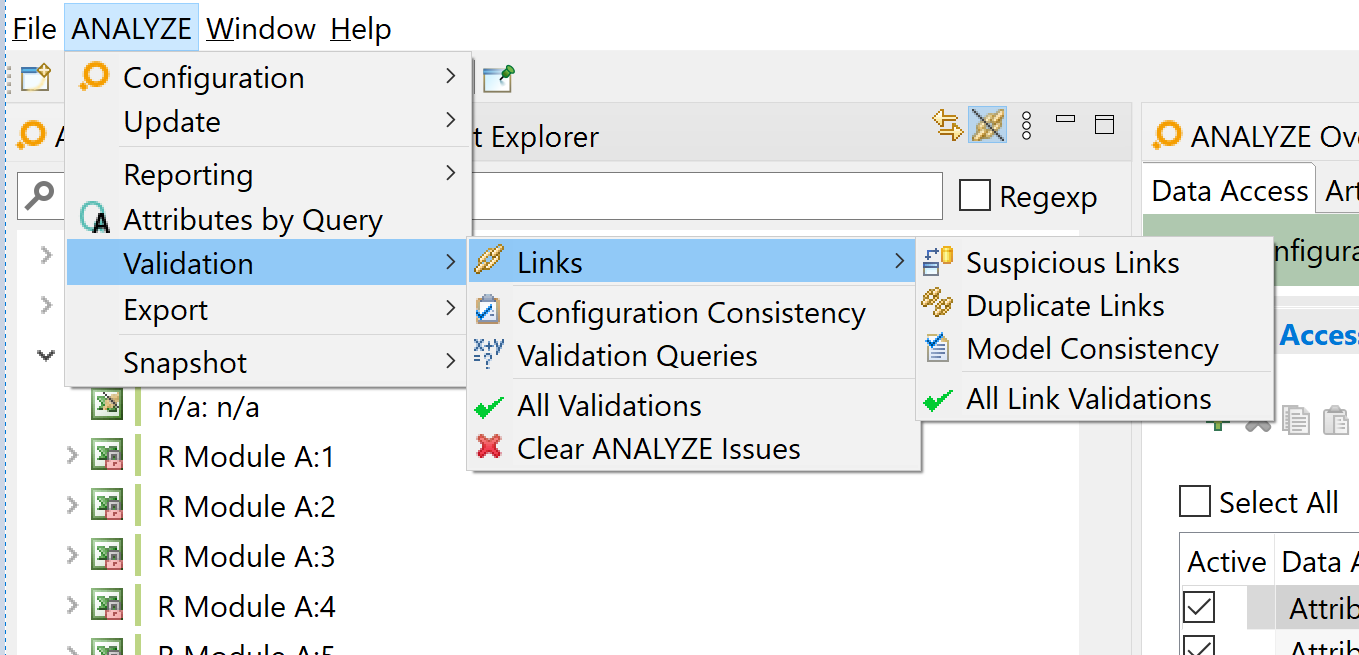
itemis ANALYZE offers several validations:
- Suspicious links validation
- Duplicate links validation
- Model consistency validation
- Configuration consistency validation
It is even possible to define your custom validation in the form of validation queries.
The results of a validation are displayed in a dialog:
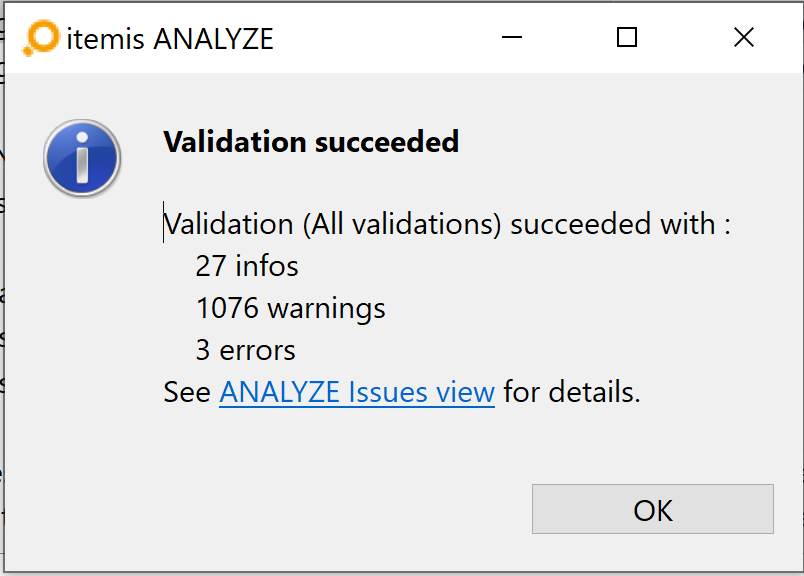
Encountered issues are displayed in ANALYZE Issues.
Suspicious links validation Copy link to clipboard
Links are created between artifacts. However, the artifacts which these links refer to might be changed after the links were created. These artifact changes might affect links. The link itself can be changed, too, e.g., by modifying its attributes. The suspicious link validation identifies these changes.
A link is called suspicious if one or both linked artifacts have been changed in a significant way. ANALYZE uses a core model that includes all trace data. To maintain a valid model, ANALYZE checks if there are no violations regarding model consistency. As artifacts or links are changed, ANALYZE checks if these changes do not result in conflicts, e.g., the name and type of an artifact or link must be set and resolved. Otherwise a precise mapping is not possible.
Detecting suspicious artifact changes Copy link to clipboard
Many, but not all, artifacts have a version . If that version changes, all links referring to that artifact version become suspicious.
However, it is up to each particular artifact type whether and how it supports the notion of a version. A few examples:
- Each file in a filesystem has a „last-modified” timestamp which could be used to indicate the version. As long as this timestamp doesn’t change, the file’s version remains the same. However, if the file’s contents is modified – and thus the „last-modified” timestamp, too –, the suspicious link validation would consider all links referring to that file being suspicious, no matter how small the change.
- The artifact version is mapped to a certain location in, say, a Microsoft Word file. The document’s author manually maintains a version number in that location. This way the artifact version is equal to whatever the author provided. It is up to the author’s discretion whether to update the version or not, depending on the kind of change he makes to the document.
- Certain artifact types might offer no version information at all, like for example Java artifacts provided by the the Eclipse Java (JDT) adapter.
Anyway, it is always the link’s responsibility whether and how to take any version information into account, see below.
In order to find artifact changes resulting in suspicious links, the validator compares
- the version information derived from the artifact itself to
- the version information that has been stored in the link at some point in time before.
If these pieces of version information are not equal the link becomes suspicious.
Detecting suspicious link changes Copy link to clipboard
While analyzing suspicious links, three different kinds of suspiciousness are checked:
- Local links with version are links that hold their artifacts' version information. This information has been gathered before and resides in the link now. Such links are typically stored locally, e.g., in a native file, see section "Native File". Checking a link for being suspicious or not is done by retrieving the current version of an artifact and comparing it to the corresponding version stored in the link. This is done for both A and B artifacts. If at least one of the comparisons results in inequality, the link is suspicious.
- Derived links are stored partially in the storage. The actual link data is defined by the configuration and defines which pieces of information in the linked artifacts are available for suspicious validation. The Excel storage is an example for such links. The link attributes are based on attributes of the linked element, and the values of these attributes are copied to cells in the Excel file during link creation. The link becomes suspicious if either the value of the cell changes (change in Excel), or if the value of one (or several) of the linked artifact’s attributes changes (change in the opposite artifact).
- Externally suspicious links are fetched from a storage which supports its own meaning of suspicious links. This information can be extracted. At the moment the PTC Integrity adapter creates such derived links and PTC Integrity provides information about suspicious traces itself.
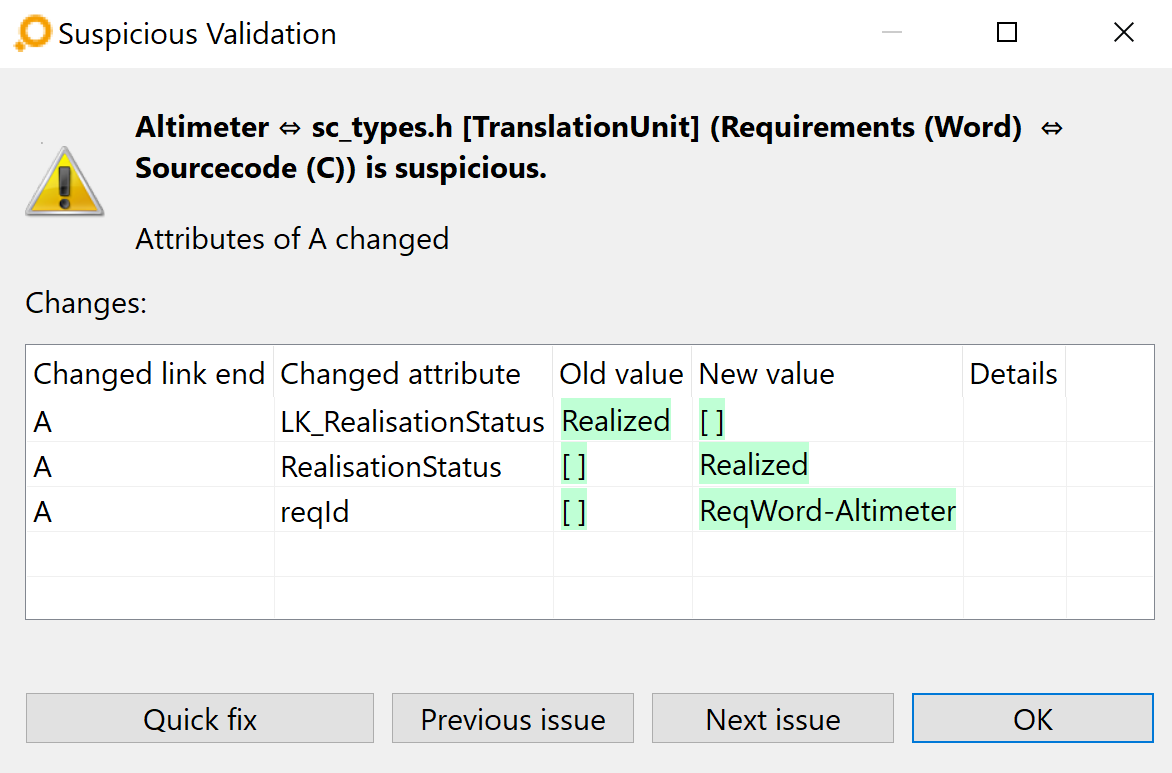
Getting detailed information on suspicious links Copy link to clipboard
When suspicious link warnings are reported in the ANALYZE Issues view, it is possible to get detailed information about a particular link by double-clicking on its corresponding line in the view. A dialog showing the link details opens. For each changed attribute of the link and of any changed artifact A or B, the dialog displays the previous and the current value. If the changed text for an attribute is too long or consists of several lines, you can click on the Show details hypertext link to open a full-screen comparison dialog. Clicking on the Quick fix button opens a dialog showing the available options to fix the issue.
Duplicate links Copy link to clipboard
There can be several links of the same link type between the same artifacts. We call these links duplicate links. ANALYZE warns users on creation of duplicate links, but generally allows them. Other duplicate links can be derived by the tool-specific adapters. Since duplicate links are often undesired, ANALYZE offers a validation to check for their existence. Duplicate links that are stored in different locations, have different attribute values, or different versions of their attributes are called similar links.
Configuration consistency Copy link to clipboard
Changes to the configuration influence the whole setup. Thus, changing the configuration may lead to type mismatches or wrong usage of adapters. The substitution of a data access could result in a type mismatch, e.g., a C file can not be accessed via an Excel adapter.